Let’s get one thing straight: quantum computing isn’t coming to save your Wi-Fi signal or make your Netflix load faster. It’s coming to rip a hole in the fabric of digital security so deep that everything you know about “safe” browsing will become a punchline.
And then? It’ll fix the mess it created.
I’ve been watching this space for years, and here’s what most people miss: we are about 10-15 years away from the single most disruptive technology event since the invention of the transistor. The hype is real, but the timeline is messy. Let me explain why quantum computing will break the internet, and how it’s the only thing that can save it.
The Encryption Apocalypse You Didn’t See Coming
You know all those little padlock icons in your browser? The ones that make you feel warm and fuzzy when you’re buying socks online at 2 AM?
They’re built on math that quantum computers will crack like a cheap egg.
Here’s the brutal truth: every modern encryption standard — RSA, ECC, AES in certain modes — relies on problems that classical computers find impossibly hard. Multiplying two huge prime numbers is easy. Factoring their product back into those primes? That takes a classical computer longer than the age of the universe for a sufficiently large number.
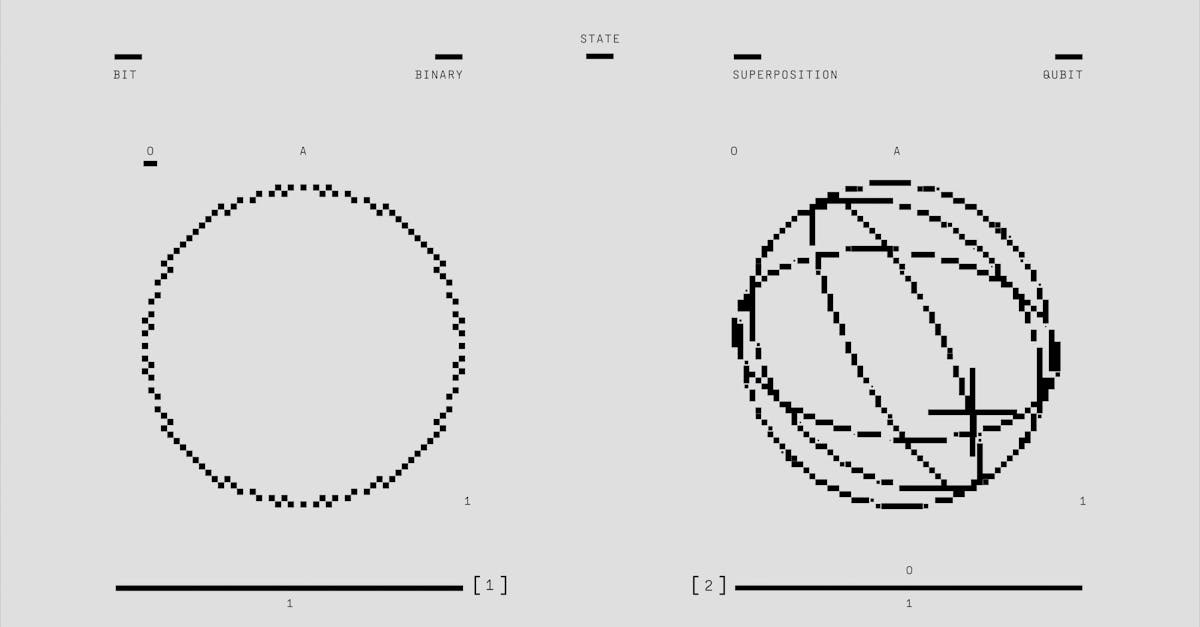
But a quantum computer with enough stable qubits doesn’t play by those rules. It uses something called Shor’s algorithm to factor those numbers in polynomial time. In plain English: a powerful enough quantum machine could break RSA-2048 encryption in seconds.
I’ve talked to cryptographers who literally lose sleep over this. One told me, “We’re building a digital house of cards, and quantum is the sneeze.”
Every password, every secure message, every blockchain transaction, every government secret — all of it becomes public record the moment someone builds a general-purpose quantum computer with 4,000+ logical qubits.

Why Your Bank Should Be Terrified Right Now
Let me share something personal: I used to work in fintech. I’ve seen the back-end security systems that keep your money safe. They’re impressive. They’re multi-layered. They’re completely vulnerable to a quantum attack.
The scary part? Harvest now, decrypt later attacks are already happening. Nation-state actors are scooping up encrypted traffic today — your emails, your bank transfers, your medical records — and storing them. They’re waiting. The moment quantum computers become operational, they’ll decrypt everything retroactively.
Your private conversations from 2025? Public in 2038.
This isn’t conspiracy theory. The NSA, China, and every major intelligence agency are already investing billions in quantum capabilities. The internet as we know it — a place where we transact, trust, and share secrets — has an expiration date.
And most people have no idea.
The Real Timeline: When the Hammer Drops
I hate tech predictions that sound like astrology, so I’ll give you the honest picture. Quantum supremacy — where a quantum computer does something no classical computer can — was achieved in 2019 by Google’s Sycamore processor. But that was a parlor trick: solving a contrived problem nobody cares about.
The real milestone is fault-tolerant quantum computing — machines that can run Shor’s algorithm without error-correcting overhead collapsing the whole thing.
Here’s my rough timeline based on talking to researchers and reading the tea leaves:
- 2025-2028: Quantum advantage in narrow domains — drug discovery, materials science, optimization. No threat to encryption yet.
- 2028-2032: First demonstrations of quantum error correction at scale. Logical qubits become viable. The panic begins.
- 2032-2038: A general-purpose quantum computer cracks RSA-2048. The internet breaks.
The Secret Savior: Post-Quantum Cryptography
Here’s the plot twist: the same quantum mechanics that breaks encryption also enables unbreakable encryption.
It’s called post-quantum cryptography (PQC) — new mathematical problems that quantum computers can’t efficiently solve. The National Institute of Standards and Technology (NIST) has already selected four algorithms for standardization. They’re not perfect, but they’re a damn sight better than what we have now.
The most promising ones are based on lattice-based cryptography. Think of it like this: classical encryption is like locking a door with a combination lock. Quantum computing can brute-force the combination. Lattice-based crypto is more like building a maze where the walls keep shifting — even a quantum computer gets lost.
But here’s the kicker: migrating the entire internet to PQC is a logistical nightmare. Every chip, every browser, every server, every IoT device needs to be updated or replaced. We’re talking about a decade-long infrastructure overhaul that makes Y2K look like a software patch.
I’ve seen estimates that upgrading the financial sector alone will cost $20-30 billion. And that’s if we start now.
What You Can Actually Do About It (Right Now)
Look, I’m not here to scare you into burying your passwords in a lead box. But I am here to give you actionable advice that most tech bloggers won’t touch:
- Stop using services that don’t support quantum-safe crypto. If your VPN or messaging app isn’t at least testing PQC integration by 2026, switch. Signal and Apple have already started.
- Diversify your crypto assets. Bitcoin’s signature scheme (ECDSA) is quantum-vulnerable. No, quantum won’t break SHA-256 for mining, but it will break wallet signatures. Look into quantum-resistant cryptos like QRL or projects migrating to PQC.
- Assume nothing is private forever. That email you sent last week? Treat it like a postcard. Because in 15 years, it might as well be.

The Bottom Line
Quantum computing isn’t a future problem. It’s a present-day problem with a delayed deadline.
The internet will break. The only question is whether we’ll have rebuilt it with stronger foundations before the collapse. The good news? The smartest minds in cryptography, from NIST to Google to IBM, are already working on the fix. The bad news? Bureaucracy moves slower than quantum algorithms.
So here’s my challenge to you: stop treating quantum computing like a sci-fi curiosity. Start asking your bank, your cloud provider, your government what their post-quantum migration plan is. If they don’t have one, they’re not taking your security seriously.
The quantum leap is coming. Will you be ready when the internet breaks — and rebuilds itself?